
Personal privacy and device security are two ever-important concerns in an increasingly digital world. Where there is personal, private, and potentially important information being stored, there is always someone out there who seeks to use it for personal gain. Harmless or not, keeping your information and devices locked down is never a bad idea. It’s always smart to keep wandering eyes out of your sensitive information, even if you have nothing to hide.
Fortunately, there is an increasing number of ways to beef up security your mobile devices. Most of thesecurity measures are straightforward and take just seconds to activate, while others may take a little effort to setup and might even add a few seconds to logging into your devices, apps, or services each time, but they will make it significantly harder for your someone to gain access to your accounts or hardware.
Below, you will find some very helpful and, more importantly, simple smartphone security tips.
Use a PIN or password
Securing your device with a simple four-digit PIN or with a password may seem like common sense, but many people simply opt out of device passwords for the sake of convenience (read: out of laziness). I’ll be the first to admit that entering a password every time I pick up my phone or tablet, although not very time-consuming, is annoying and can be frustrating if you’re trying to access something in a hurry.
However, our own Joe Levi makes a very valid point.You wouldn’t park your car and leave it unlocked, why wouldn’t you do the same for your phone?
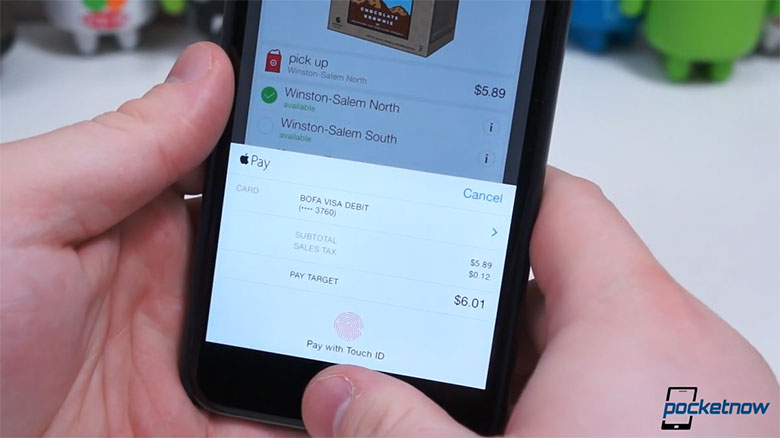 With biometric sensors on smartphones and tablets, it’s a no-brainer to at least add some level of security to your phone via a PIN or password lock. TouchID on Apple’s iOS devices is one of the best examples of streamlining the security process, but Apple’s devices aren’t the only ones with fingerprint scanners. Some say fingerprints are one of the least secure methods of authentication, since they’re easily replicated – but this isn’t Hollywood and unless you have some seriously valuable information on your devices, I doubt anyone will go through the trouble of copying your fingerprint.
With biometric sensors on smartphones and tablets, it’s a no-brainer to at least add some level of security to your phone via a PIN or password lock. TouchID on Apple’s iOS devices is one of the best examples of streamlining the security process, but Apple’s devices aren’t the only ones with fingerprint scanners. Some say fingerprints are one of the least secure methods of authentication, since they’re easily replicated – but this isn’t Hollywood and unless you have some seriously valuable information on your devices, I doubt anyone will go through the trouble of copying your fingerprint.
Think of it as a deadbolt on the front door to your home. Windows are still a vulnerability and a deadbolt won’t stop someone who knows how to use a lock pick set, but the deadbolt alone is enough to ward of most intruders. A fingerprint is no different.
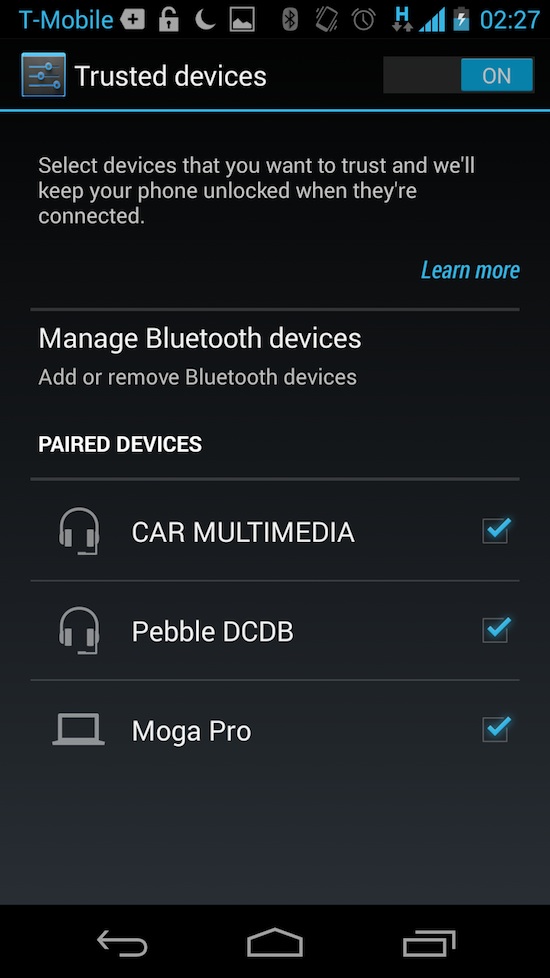 Also very helpful are third-party applications which permit access to your devices sans password when connected to certain Bluetooth device or in range of specific wireless networks. Pebble Locker, Tasker, and SkipLock are just a few examples of ways to keep your devices secure without having to constantly enter a password – but if you leave your phone behind or leave a trusted area or network, the password is immediately reenabled.
Also very helpful are third-party applications which permit access to your devices sans password when connected to certain Bluetooth device or in range of specific wireless networks. Pebble Locker, Tasker, and SkipLock are just a few examples of ways to keep your devices secure without having to constantly enter a password – but if you leave your phone behind or leave a trusted area or network, the password is immediately reenabled.
Android 5.0 and even Motorola have such features baked-in, as well. Motorola calls this feature Trusted Devices while the it’s referred to as Personal Unlocking in the latest version of Android, Lollipop.
Another one of my favorites is TimePIN (Android-only), which changes your PIN every minute of the day. Your PIN is literally the time, or some modified version of the current time or date. This keeps anyone who may see you enter your PIN from actually knowing the correct PIN and keeps your device secure with minimal effort.
A PIN or password may be a pain to enter every time you grab your device, so we rcommend differentiating lock timeouts when possible. For instance, on many Android devices, you can set the password prompt to appear immediately when you manually turn the screen off using the standby key or only after, say, five minutes when the screen times out on its own.
Either way, skipping this step nullifies almost every one of the following security steps.
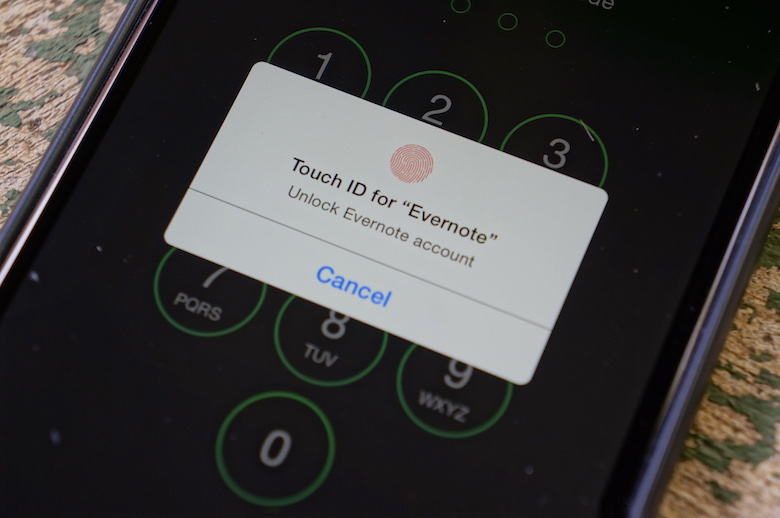
Password protect individual apps
Some applications offer their own forms of security. For example, I keep a ton of private information in Evernote and I write a lot of very personal stuff in Day One, a journaling application for iOS. Both of these applications allow you to set a PIN or password for access and, with appropriate hardware, you can use a fingerprint scanner as a form of authentication.
Other applications – like Dropbox and LastPass – which might contain sensitive information also offer password prompts to keep prying eyes out.
Use a password manager
While the standard password won’t keep users out of an account (there have been countless breaches in security wherein users’ passwords were stolen through a backdoor exploit), it’s good to use a password which is unique, very long, and not easily memorable. However, that poses a problem of its own. If it isn’t memorable, how will you remember it?
A password manager.
Personally, I use LastPass Premium which is just $12 per year, but there are plenty of services out there that offer exactly the same thing. One other notable password manager is 1Password.
Basically, I don’t actually know most of my passwords. I use LastPass to generate new passwords for me, save them to a specific account, and I copy and paste the passwords or rely on the Auto-Fill feature when I need to login to any service, either from my computer, tablets, or phones.
Frankly, this can be a very frustrating process, both to use regularly and to maintain, but once you get everything organized and figure out your own process for using a password manager, it’s well worth all the trouble.
 Also very helpful are some of the newer developments in the mobile apps. LastPass and 1Password can use integrated fingerprint scanners for authentication, and there is a pop-up fill window available for the Android version of LastPass. Whenever you come across credential fields asking for a username and password, so long as it’s setup properly (and allowed in accessibility settings), a floating LastPass window will appear and allow you to quickly auto-fill the information.
Also very helpful are some of the newer developments in the mobile apps. LastPass and 1Password can use integrated fingerprint scanners for authentication, and there is a pop-up fill window available for the Android version of LastPass. Whenever you come across credential fields asking for a username and password, so long as it’s setup properly (and allowed in accessibility settings), a floating LastPass window will appear and allow you to quickly auto-fill the information.
In iOS 8, thanks to Extensibility and new extensions, you can now use 1Password and LastPass to auto-fill within Safari.
You may still have to login to LastPass or enter a PIN (for ease of access), but it’s generally not so bad. It adds a few steps to every login, but my personal information is more secure, especially considering I don’t even know the passwords.
Two-factor authentication
If any app or service uses two-step authentication, use it. Plain and simple, this is one of the best ways to snuff out chances of someone gaining access to your online accounts. (That said, it still isn’t fool-proof.)
Believe it or not, two-step authentication isn’t as painful as it may sound. The age-old method of shooting a text message to your phone with an authentication code still works wonderfully. But there are newer ways which are not nearly as cumbersome, such as Authy or the Google Authenticator app.
 Essentially, rather than having each individual service send a text message to your phone, you can use Authy to generate new codes (every 30 seconds) from one cerntralized location. This also means that you don’t need a mobile number or SMS – or cell service, for that matter, as long as you have Wi-Fi – to get an authentication code. You can get said codes from several different sources: your tablet, phone, computer, or even your browser. Authy has a Chrome app for receiving authentication codes directly on your computer, or you can pair your phone to your computer using Bluetooth to have access to these quickly-expiring codes straight from the toolbar on your Mac (shown at right).
Essentially, rather than having each individual service send a text message to your phone, you can use Authy to generate new codes (every 30 seconds) from one cerntralized location. This also means that you don’t need a mobile number or SMS – or cell service, for that matter, as long as you have Wi-Fi – to get an authentication code. You can get said codes from several different sources: your tablet, phone, computer, or even your browser. Authy has a Chrome app for receiving authentication codes directly on your computer, or you can pair your phone to your computer using Bluetooth to have access to these quickly-expiring codes straight from the toolbar on your Mac (shown at right).
Authy will create a second layer of security for all your (compatible) logins while not making the login process much more time-consuming or difficult, which is the whole idea, right?
I was adamantly against two-factor authentication a few months ago, simply for how cumbersome and frustrating it was just to login to a few apps on your phone. I also feared setting up two-factor authentication on multiple services would be a complicated process. But it wasn’t … at all. Completely setting up Authy for my Evernote, Dropbox, Gmail, Buffer, Facebook, and LastPass accounts took about an hour in total, and logging in to each service only takes a few seconds more each time.
Joe also notes new hardware “keys” that new browsers are capable of reading. They’re just a few dollars on Amazon and can further streamline the process.
It’s well worth all the trouble and extra steps in the end.
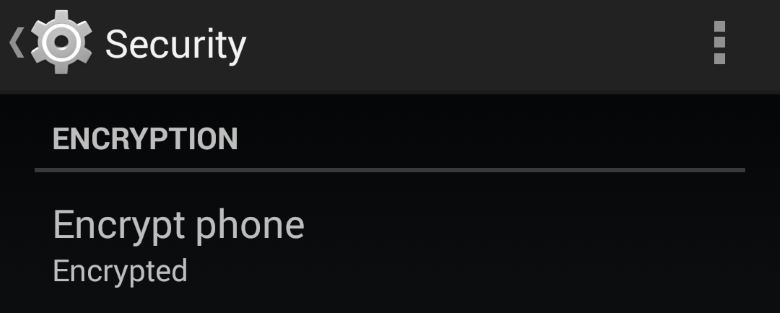
Encrypt your data and web traffic
I asked Joe for some tips for securing your device and above all, he noted it’s best to “encrypt everything you can.” On most Android phones, you can encrypt all your local storage by paying a visit to the Security section in the settings app and selecting the Encrypt Phone option.
It’s worth noting that encryption probably isn’t for everyone and there are some disadvantages to encrypting your phone. For instance, encryptioncan slow your phone down, though that’s no longer the case with Android, and if you ever want to reverse the process, your phone will have to be wiped. The process will also take quite some time to encrypt all the data on your phone, but after the initial encryption process, it will all happen in the background automatically.
The benefit, obviously, is that anyone trying to access your phone won’t be able to read the jumbled data without the decryption keys. Likewise, if you wipe your phone and sell it, whomever gets your phone next would have to both recover and decrypt the data to see what was previously on the phone.
To encrypt your web traffic, it’s best to simply use the HTTPS prefix for all web addresses. No,Incognito doesn’t secure your web activity. Though, you can also use Orbot to anonymize all your web traffic by connecting to the Tor network.
Use common sense
Finally, there are small loopholes to everything – no security measures are infallible. If there is a way for someone to extract your information and data, someone will find it. That said, most people are safe from such risks. It is best not to worry or blow security concerns out of proportion, but a basic knowledge of security and encryption is a great way to make snatching your private information more trouble than it’s worth.

That little orange square is a microSD card reader that I use to store files I don’t necessarily want on my phone.
For instance, storing sensitive documents on an encrypted SD card and using a card reader, like this one from Meenova, is a simple way to keep documents within reach but not locally stored.
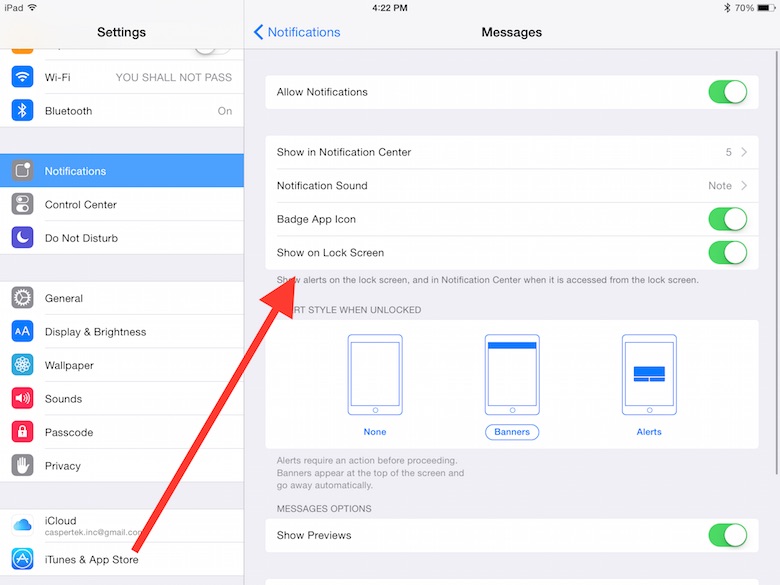
Using common sense in conjunction with many of these tips is vital. If you password lock your phone but enable the notification shade on the lock screen, you’re still leaving some information on a silver platter for prying eyes. If you connect to open Wi-Fi connections in public, you’re opening the door for a world of problems. (Seriously, this articlewill make you think twice about which wireless networks you connect to.)
Some measures, however, just aren’t worth the trouble for most people. Avoiding the public Wi-Fi at your local coffee shop would defy the whole reason for going for most people. But using even the most basic security measures is a decent enough deterrent to keep your information safe in most real world situations.



No comments:
Post a Comment